TrustZone Overview¶
REVISION HISTORY¶
| Revision No. | Description |
Date |
|---|---|---|
| 1.0 | 05/22/2023 |
1. INTRODUCTION TO SGS TRUSTZONE¶
1.1. Overview¶
ARM TrustZone is a hardware-level mandatory isolation technology that divides the execution state of the processor into two areas:
-
secure world: used for running trusted software.
-
non-secure world: used for running untrusted software.
Resources such as device hardware and memory are also divided:
-
When the CPU runs in the non-secure world, it can only access non-secure resources.
-
When the CPU runs in the secure world, it can access both secure resources and non-secure resources.
ARM TrustZone is designed to prevent consumers from attacking through operating system or application program vulnerabilities, reading and writing hardware and software resources. SGS chip follows the technology and specifications of ARM TrustZone to realize the function of system security.
1.2. SGS TrustZone Hardware¶
For more introduction on the TrustZone hardware architecture, please refer to the official document (trustzone_security_whitepaper.pdf) available from: https://developer.arm.com/documentation/PRD29-GENC-009492/latest/
The main hardware modules of SGS TrustZone involve CPU, secure interrupt group, TZIMI, TZEMI and TZSP.
1.2.1 CPU Security¶
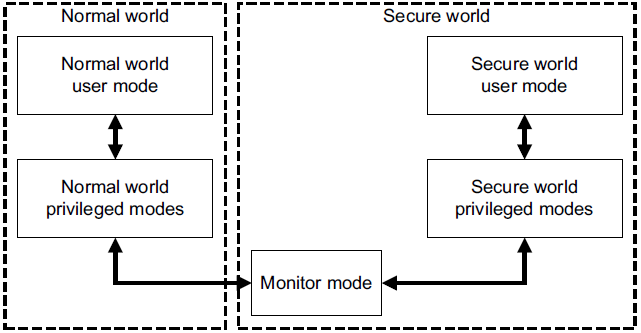
Figure 1: S/NS-wrold
A physical CPU core is divided into two virtual CPU cores: one is a secure core and the other is a non-secure core. In the process of switching between secure and non-secure cores, the CPU needs to enter the monitor mode first. ARM provides an SMC (Secure Monitor Call) instruction. After this instruction is executed, the CPU will switch to the monitor mode. The CPU in the secure world can switch to the Secure Monitor mode through the SMC instruction. The specific handling function of the SMC soft interrupt is implemented in BL31. The SMC interrupt handling function will control whether to switch the cortex to the secure world state or the non-secure world state according to whether the sent command belongs to the request of the secure side or the non-secure side. The same is true for the process of switching from the secure world to the non-secure world.
There are two cases in the transition from non-secure world to secure world:
-
Non-secure world calls SMC while executing the code.
-
Non-secure world encounters an interrupt in group0 while executing the code.
There are two cases in the transition from secure world to non-secure world:
-
Secure world calls SMC while executing the code.
-
Secure world encounters an interrupt in group1 while executing the code.
1.2.2 Interrupt Security¶
Under the TrustZone design, all interrupts are divided into two groups:
-
Group 0
-
Group 0 interrupt is always secure.
-
the interrupt can be issued in the form of FIQ or IRQ.
-
The interrupt is generally issued to OPTEE OS.
-
-
Non-secure Group 1
-
Group 1 interrupt is always non-secure.
-
The interrupt is always issued in the form of IRQ.
-
The interrupt is generally issued to Linux OS.
-
SGS chip designates each interrupt as one of the two groups through software presets to ensure that secure interrupts can only be processed by trusted OS.
1.2.3 DRAM Security¶
Basically all CPUs and IPs in the SGS chip can access DDR. The entire DDR can be divided into 17 regions at most. The secure access of DRAM is guaranteed by TZEMI. TZEMI divides all IPs that can access DDR into S/NS attributes, and each DDR region is also divided into S/NS attributes by TZEMI from the hardware design. When the CPU and IP (Master) access the DRAM region (Slave), TZEMI will judge the security attributes to determine whether the access is legal.
1.2.4 SRAM Security¶
The masters that can access SRAM in SGS chip include: MCU/VENC0/AESDMA/SD30/BDMA/SDIO/FCIE. The entire SRAM can be divided into 2 regions at most. The secure access of SRAM is guaranteed by TZIMI. TZIMI divides IMI clients into S/NS attributes, and each SRAM region is also divided into S/NS attributes by TZIMI from the hardware design. When the IMI client (Master) accesses the IMI region (Slave), TZIMI will judge the security attributes to determine whether the access is legal.
1.2.5 IP Security¶
The masters that can access IP in SGS chip includes: CPU/CMDQ0/CMDQ1/VENC-RISVC/ISP0-CMDQ/debug port, and all accessed IPs are allocated in different RIU banks. The secure access of IP is guaranteed by TZSP. TZSP divides RIU master IPs into S/NS attributes, and each RIU bank is also divided into S/NS attributes by TZSP from the hardware design. When the RIU master IP accesses the RIU bank (Slave), TZSP will judge the security attributes to determine whether the access is legal.
1.3. OP-TEE Software Architecture¶
OP-TEE (Open Portable Trusted Execution Environment) is an open source portable trusted execution environment. Based on the hardware isolation and security monitoring mechanism of TrustZone technology, TEE runs in the secure domain of the TrustZone, isolated from the non-secure domain of the TrustZone in which the ordinary operating systems (such as Linux/rtk/freertos) run.
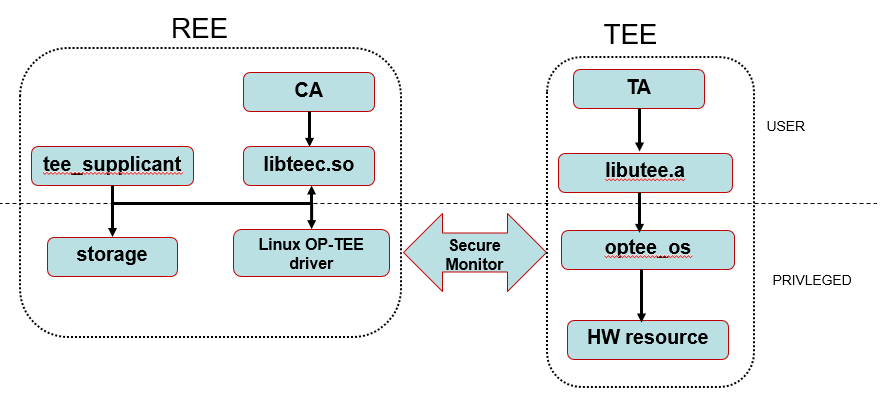
Figure 2: Software Architecture
The software system running on the SGS chip can be divided into two parts: TEE and REE.
REE (Rich Execution Environment): Refers to the ordinary operating system execution environment, i.e. Linux.
TEE (Trusted Execution Environment): Refers to the trusted execution environment, i.e. OP-TEE.
TA (trust applicant): Refers to the application running on OP-TEE.
CA (client applicant): Refers to the application running on Linux.
libteec library: An interface implementation provided by OP-TEE for users to call at the Linux userspace level.
tee_supplicant: After startup, it runs as a background program in Linux, and provides OP-TEE with operations on the REE end (Linux) file system in a way similar to C/S. The main function of tee_supplicant is to enable OP-TEE to use tee_supplicant to access the resources in the REE side (Linux) file system, such as loading the TA image stored in the file system to the TEE.
OP-TEE driver: The main function is to act as a bridge for data interaction between REE and TEE. The tee_supplicant and libteec call interfaces first fall into the OP-TEE driver get_invoke_func function code of the kernel space through system calls, and finally switch to monitor by issuing smc, and send the data passed down when calling the interfaces to the secure world for processing.
libutee library: In OP-TEE, userspace interfaces are generally defined in the form of utee_xxx_xxx. These interfaces uniformly defined by GP (Gloable Platform) are generally implemented in libutee.a library, and the corresponding system calls are syscall_xxx_xxx.
HW resource: Currently, resources protected by default on the SGS platform software are as follows:
-
MIIC0
-
OTP ctrl
-
TF-A and TEE OS memory (the DDR segment marked in yellow below)

Figure 3: MIU Layout
For more details on the optee software architecture, please visit: https://optee.readthedocs.io/en/latest/index.html
1.4. SGS TrustZone Startup Process¶
According to the ARM architecture definition, the entire system is divided into four operating levels, namely USR, SVC, HYP, and MON, the software startup process corresponding to the SGS platform is as follows:
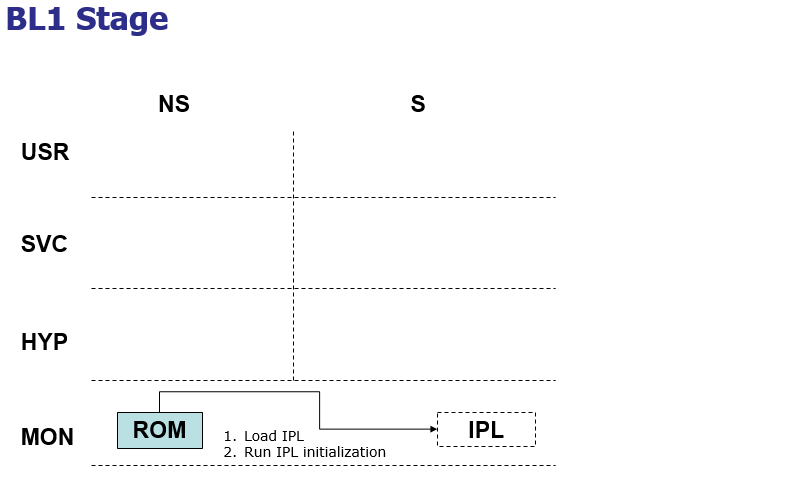
Figure 4: boot flow-1
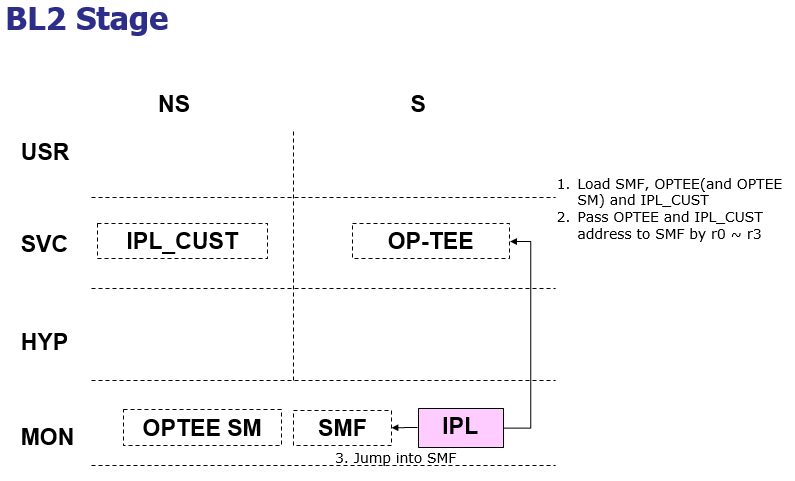
Figure 5: boot flow-2
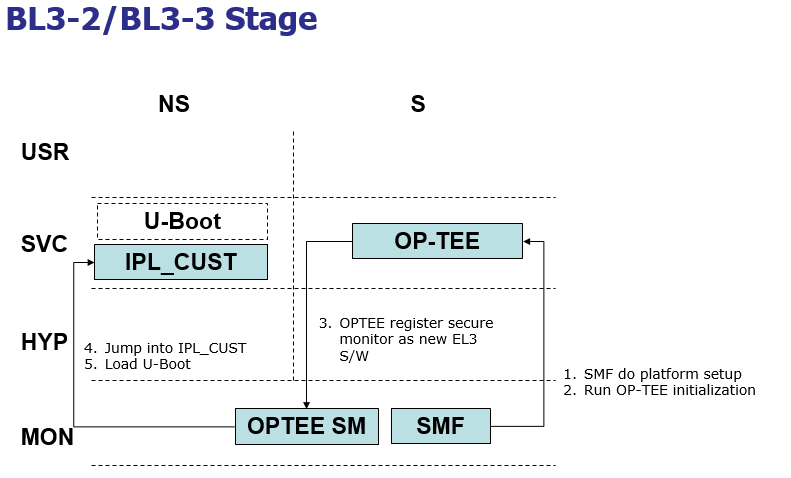
Figure 6: boot flow-3
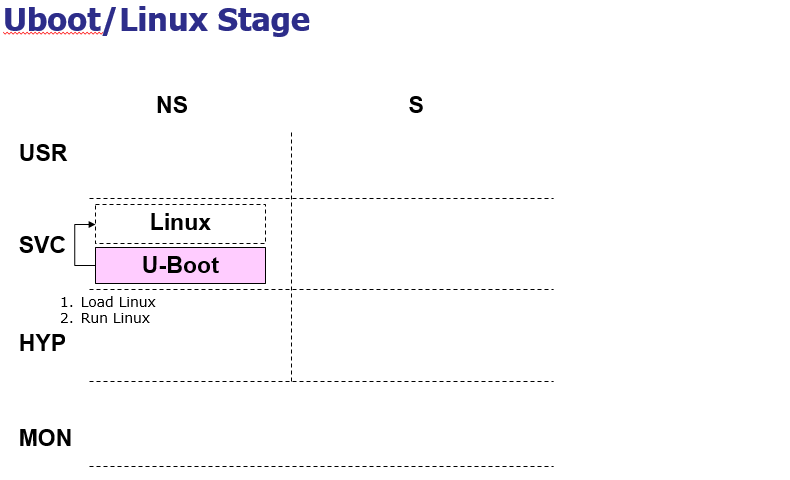
Figure 7: boot flow-4
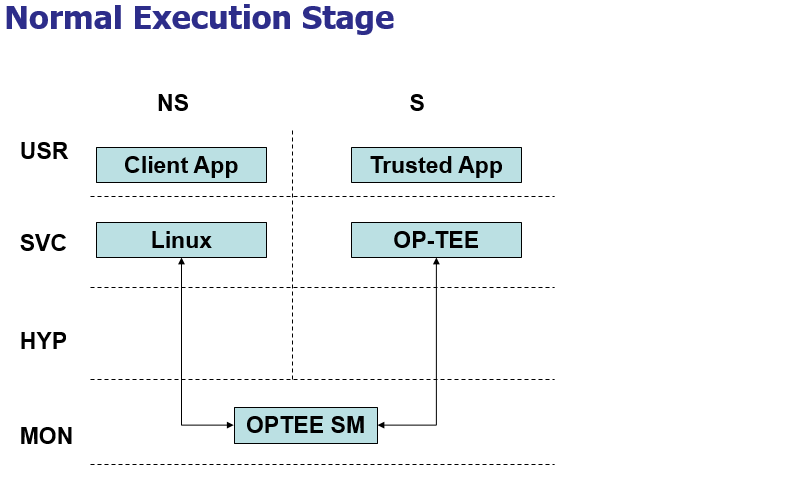
Figure 8: boot flow-5