OTP Usage Reference¶
REVISION HISTORY¶
| Revision No. | Description |
Date |
|---|---|---|
| 1.00 | 06/09/2025 | |
| 1.01 | 11/17/2025 |
1. Overview¶
1.1 What is OTP¶
OTP (One-Time Programmable) is a one-time programmable memory with the following characteristics:
- One-time write: Each bit can only be programmed from 0 to 1 once, cannot be changed from 1 back to 0
- Non-volatile: Data is retained after power loss
- High security: Stored information cannot be tampered with, suitable for storing sensitive data such as keys and configurations
- Hardware-level protection: Provides LOCK (write protection) and BLOCK (read protection) functions
Important Notes:
- Each bit in OTP can only be programmed once. Once set to 1, it cannot be set back to 0
- Programming the same data to the same location is not allowed more than three times
- Please perform programming operations only when you are certain it is necessary!
1.2 OTP Usage Scenarios¶
OTP is mainly used for the following scenarios:
- Secure Boot: Store public keys, encryption keys to ensure system boot security
- Key Management: Save AES, RSA and other encryption keys
- Device Identification: Store UUIDs, device IDs and other unique identifiers
- Security Protection: Configure anti-attack, anti-tampering and other security functions
- Debug Protection: Set access control for debug interfaces
- User Data: Store customer-defined configuration information
1.3 How to Use OTP¶
1.3.1 Basic Operation Commands¶
- Read OTP:
otpctrl -r <command_id> - Write OTP:
otpctrl -w <command_id> <offset> <data>
1.3.1.1 Command Parameter Description¶
command_id (Command ID):
- Used to identify different OTP storage areas, each command_id corresponds to a specific functional area
- For example:
0x0corresponds to RSA public key N value storage area,0x2corresponds to secure boot switch - The value range of command_id and corresponding functions are detailed in the OTP field description table in subsequent sections
offset (Address Offset):
- Represents the byte offset within the specified command_id area
- Offset increments in 4-byte units (0, 4, 8, 12, ...)
- For example: offset 0x0 represents the starting position of the area, offset 0x4 represents the 5th byte position
data (Data):
- 32-bit data to be written, expressed in hexadecimal format
- Data size is fixed at 4 bytes (32 bits)
- For example:
0xFFFFFFFFrepresents writing 32 ones
1.3.1.2 Command Usage Examples¶
Example 1: Enable Secure Boot Function
# Write secure boot switch (command_id=0x2, offset=0x0, data=0xFFFFFFFF)
otpctrl -w 0x2 0x0 0xFFFFFFFF
Example 2: Configure RSA Public Key (Multiple Writes)
# Write the first part of RSA public key N value (command_id=0x0)
otpctrl -w 0x0 0x0 0x58653431 # offset=0x0, write bytes 1-4
otpctrl -w 0x0 0x4 0x06ba8f4a # offset=0x4, write bytes 5-8
otpctrl -w 0x0 0x8 0x5caee61a # offset=0x8, write bytes 9-12
# ... Continue writing the complete 512-byte RSA N value
# Write RSA public key E value (command_id=0x1, only 4 bytes)
otpctrl -w 0x1 0x0 0x00010001
Example 3: Read Verification
# Read secure boot status
otpctrl -r 0x2
# Read RSA public key E value for verification
otpctrl -r 0x1
1.3.2 OTP Modification Process¶
- Confirm modification content: Clearly identify the functions and parameters to be configured
- Prepare data: Generate necessary data such as key files and certificates
- Convert to programming format: Use tools to convert raw data into otpctrl commands
- Execute programming: Run programming commands in UBOOT environment
- Verify results: Read OTP to confirm successful programming
- Enable protection (optional): Enable LOCK or BLOCK protection as needed
1.3.3 Complete Example: Configure RSA Public Key and Enable Secure Boot¶
The following is a complete OTP configuration example demonstrating how to configure RSA public key and enable secure boot function:
Step 1: Prepare RSA Public Key File
Assuming you have an RSA public key file rsa-public.pem:
-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA...
-----END PUBLIC KEY-----
Step 2: Convert to Programming Format
cd project/image/security_boot_tools/tools/
./key_proc.py --exportkey_reverse --rsa=public.pem
This command will generate an rsaKey.txt file containing the otpctrl commands needed for programming.
Step 3: Enter UBOOT Environment
Restart the device and enter the UBOOT command line interface.
Step 4: Program RSA Public Key N Value
Copy the RSA N-Key part from rsaKey.txt to UBOOT for execution:
####### RSA N-Key ########
otpctrl -w 0x0 0x0 0x58653431;otpctrl -w 0x0 0x4 0x06ba8f4a;otpctrl -w 0x0 0x8 0x5caee61a;otpctrl -w 0x0 0xc 0x1912648d;...
Note: Due to UBOOT command line cache limitations, it is recommended to execute in batches, with no more than 16 commands per batch.
Step 5: Program RSA Public Key E Value
####### RSA E-Key ########
otpctrl -w 0x1 0x0 0x00010001
Step 6: Verify Programming Results
# Read RSA N value
otpctrl -r 0x0
# Read RSA E value
otpctrl -r 0x1
Step 7: Enable Secure Boot Function
otpctrl -w 0x2 0x0 0xFFFFFFFF
Step 8: Verify Secure Boot Status
otpctrl -r 0x2
Step 9: Restart Device for Verification
Restart the device and confirm that the system starts normally and the secure boot function is effective.
2. Detailed OTP Field Description¶
The following provides detailed descriptions of each OTP field based on usage scenarios, including functions, command_ids and specific usage methods. Each scenario provides specific command examples corresponding to the basic operation commands introduced earlier.
2.1 OTP Fields Related to Secure Boot¶
Usage Scenario: Enable the system's secure boot function to ensure only digitally signed firmware can run, protecting the system from malicious software attacks.
For IFord system chips, if customers use the security boot function, they need to pay attention to the following OTP contents:
| OTP | command ID | length(byte) | Permission | Description |
|---|---|---|---|---|
| OTP_RSA_N | 0X00 | 512 | Read/Write | Save the N value of RSA public key used for IPL signature verification |
| OTP_RSA_E | 0X01 | 4 | Read/Write | Save the E value of RSA public key used for IPL signature verification |
| OTP_SECURITY_BOOT | 0X02 | 4 | Read/Write | Security boot function switch, needs to be enabled after confirming RSA/AES keys are correctly programmed |
| OTP_RSA_KEY_LOCK | 0X03 | 4 | Read/Write | LOCK action for RSA Public Key fields in OTP, cannot be modified after LOCK, customers can use as needed |
| OTP_RSA_KEY_BLOCK | 0X04 | 4 | Read/Write | BLOCK action for RSA Public Key fields in OTP, CPU cannot read RSA Public Key from OTP after BLOCK, customers can use as needed |
| OTP_KEY1 | 0X05 | 16 | Read/Write | 1st AES128 key |
| OTP_KEY2 | 0X06 | 16 | Read/Write | 2nd AES128 key, can also be combined with OTP_KEY1 to form the 1st AES256 key |
| OTP_KEY3 | 0X07 | 16 | Read/Write | 3rd AES128 key |
| OTP_KEY4 | 0X08 | 16 | Read/Write | 4th AES128 key, can also be combined with OTP_KEY3 to form the 2nd AES256 key |
| OTP_KEY5 | 0X09 | 16 | Read/Write | 5th AES128 key |
| OTP_KEY6 | 0X0A | 16 | Read/Write | 6th AES128 key, can also be combined with OTP_KEY5 to form the 3rd AES256 key |
| OTP_KEY7 | 0X0B | 16 | Read/Write | 7th AES128 key |
| OTP_KEY8 | 0X0C | 16 | Read/Write | 8th AES128 key, can also be combined with OTP_KEY7 to form the 4th AES256 key |
| OTP_AES_KEY1_LOCK | 0X0D | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY1_BLOCK | 0X0E | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_AES_KEY2_LOCK | 0X0F | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY2_BLOCK | 0X10 | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_AES_KEY3_LOCK | 0X11 | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY3_BLOCK | 0X12 | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_AES_KEY4_LOCK | 0X13 | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY4_BLOCK | 0X14 | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_AES_KEY5_LOCK | 0X15 | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY5_BLOCK | 0X16 | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_AES_KEY6_LOCK | 0X17 | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY6_BLOCK | 0X18 | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_AES_KEY7_LOCK | 0X19 | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY7_BLOCK | 0X1A | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_AES_KEY8_LOCK | 0X1B | 4 | Read/Write | Cannot be modified after LOCK, non-zero bits in 16-byte OTP content cannot be set to 1, customers can use as needed |
| OTP_AES_KEY8_BLOCK | 0X1C | 4 | Read/Write | Cannot be modified after BLOCK, only HW aesdma can access while CPU cannot, customers can use as needed |
| OTP_ROM_SELECT_AES_KEY | 0X24 | 4 | Read/Write | Select which AES key in OTP to decrypt IPL, once this OTP is written, IPL must use AES encryption |
| OTP_ROM_SELECT_AES_KEY_LOCK | 0X25 | 4 | Read/Write | Cannot be modified after LOCK for OTP_ROM_SELECT_AES_KEY |
| OTP_RSA_KEY_LEN | 0X2F | 4 | Read/Write | Must be programmed when using RSA4096 signing. Not needed if using RSA2048 signing |
The programming methods for each OTP field are illustrated as follows.
2.1.1 Configure RSA Public Key N and E Values (OTP_RSA_N: 0x0, OTP_RSA_E: 0x1)¶
For an existing rsa-public.pem file, you need to first convert the PEM format to a format suitable for programming. Use the following command to generate rsaKey.txt, where the commands in rsaKey.txt are used to write OTP in UBOOT.
cd project/image/security_boot_tools/tools/
./key_proc.py --exportkey_reverse --rsa=public.pem
For example, the converted rsaKey.txt content from an existing PEM file is as follows, which can be directly copied and pasted into the UBOOT menu command line for execution:
####### RSA N-Key ########
otpctrl -w 0x0 0x0 0x58653431;otpctrl -w 0x0 0x4 0x06ba8f4a;otpctrl -w 0x0 0x8 0x5caee61a;otpctrl -w 0x0 0xc 0x1912648d;otpctrl -w 0x0 0x10 0xb3b77f1c;otpctrl -w 0x0 0x14 0xd116e973;otpctrl -w 0x0 0x18 0x74f82967;otpctrl -w 0x0 0x1c 0xf85d78e8;otpctrl -w 0x0 0x20 0x55a92d7a;otpctrl -w 0x0 0x24 0xf807ef92;otpctrl -w 0x0 0x28 0xeaca7ab8;otpctrl -w 0x0 0x2c 0x2d33149a;otpctrl -w 0x0 0x30 0xc47f6cfb;otpctrl -w 0x0 0x34 0x99d0fb2b;otpctrl -w 0x0 0x38 0xb94e529f;otpctrl -w 0x0 0x3c 0x09d1e66a;
otpctrl -w 0x0 0x40 0x93614b62;otpctrl -w 0x0 0x44 0x40db5115;otpctrl -w 0x0 0x48 0x4d37ec4c;otpctrl -w 0x0 0x4c 0xd7ac36da;otpctrl -w 0x0 0x50 0x8bbef7bb;otpctrl -w 0x0 0x54 0x459ffe82;otpctrl -w 0x0 0x58 0xea5aa7ed;otpctrl -w 0x0 0x5c 0x979ac988;otpctrl -w 0x0 0x60 0xd9ad7843;otpctrl -w 0x0 0x64 0xb086c544;otpctrl -w 0x0 0x68 0x75248853;otpctrl -w 0x0 0x6c 0xd0c61f34;otpctrl -w 0x0 0x70 0xd4fd028a;otpctrl -w 0x0 0x74 0x93037bd3;otpctrl -w 0x0 0x78 0x2b3cd0e2;otpctrl -w 0x0 0x7c 0x12b49f2d;
otpctrl -w 0x0 0x80 0x72fc0405;otpctrl -w 0x0 0x84 0xc1fb6cfd;otpctrl -w 0x0 0x88 0xb42fb860;otpctrl -w 0x0 0x8c 0xa06e8c6e;otpctrl -w 0x0 0x90 0x43870bc3;otpctrl -w 0x0 0x94 0xb97ebe88;otpctrl -w 0x0 0x98 0x45113bd1;otpctrl -w 0x0 0x9c 0xb7974436;otpctrl -w 0x0 0xa0 0x47c3d001;otpctrl -w 0x0 0xa4 0x3611716d;otpctrl -w 0x0 0xa8 0x67abc2d5;otpctrl -w 0x0 0xac 0x773ac1cd;otpctrl -w 0x0 0xb0 0x7d1ee609;otpctrl -w 0x0 0xb4 0xc72e97ee;otpctrl -w 0x0 0xb8 0x91af8bd5;otpctrl -w 0x0 0xbc 0xd516243d;
otpctrl -w 0x0 0xc0 0x949b2522;otpctrl -w 0x0 0xc4 0x3d73c4d7;otpctrl -w 0x0 0xc8 0xcf2fde53;otpctrl -w 0x0 0xcc 0xbd35d242;otpctrl -w 0x0 0xd0 0x2362de0f;otpctrl -w 0x0 0xd4 0x8d9f7418;otpctrl -w 0x0 0xd8 0x861f69d5;otpctrl -w 0x0 0xdc 0x0736f5ff;otpctrl -w 0x0 0xe0 0x7655b44e;otpctrl -w 0x0 0xe4 0x06198429;otpctrl -w 0x0 0xe8 0xe0975a88;otpctrl -w 0x0 0xec 0x6fcec320;otpctrl -w 0x0 0xf0 0x49480b57;otpctrl -w 0x0 0xf4 0xea4a5ee3;otpctrl -w 0x0 0xf8 0x6502ddee;otpctrl -w 0x0 0xfc 0xd6d17ae2;
####### RSA E-Key ########
otpctrl -w 0x1 0x0 0x00010001
Note: Due to the limited buffer length of the UBOOT menu command line, you cannot directly copy and paste 64 otpctrl commands as a single execution. It is recommended to execute them in at least 4 batches.
2.1.2 Enable Secure Boot Function (OTP_SECURE_BOOT: 0x2)¶
After confirming that RSA/AES keys are programmed, enable the security boot function (effective on next boot):
otpctrl -w 0x2 0x0 0xFFFFFFFF
Check if security boot function is enabled:
otpctrl -r 0x2
2.1.3 RSA Key Write Protection and Read Protection (OTP_RSA_KEY_LOCK: 0x3, OTP_RSA_KEY_BLOCK: 0x4)¶
Optional operation, customers can use as needed.
Confirm LOCK and BLOCK of RSA key (effective on next boot):
otpctrl -w 0x3 0x0 0xFFFFFFFF
otpctrl -w 0x4 0x0 0xFFFFFFFF
Check if LOCK and BLOCK are enabled:
otpctrl -r 0x3
otpctrl -r 0x4
2.1.4 Configure AES Encryption Keys (OTP_AES128_KEY: 0x5~0xC)¶
If customers use the signature + encryption function of security boot, programming AES KEY is a necessary operation.
For making AES128 KEY:
echo '000102030405060708090A0B0C0D0E0F' | xxd -r -ps > aesKey128_1.bin
Program AES key to OTP_KEY1 position:
otpctrl -w 0x5 0x0 0x03020100
otpctrl -w 0x5 0x4 0x07060504
otpctrl -w 0x5 0x8 0x0B0A0908
otpctrl -w 0x5 0xC 0x0F0E0D0C
For making AES256 KEY:
echo '000102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F' | xxd -r -ps > aesKey256_1.bin
Program AES key to OTP_KEY1 and OTP_KEY2 positions:
otpctrl -w 0x5 0x0 0x03020100
otpctrl -w 0x5 0x4 0x07060504
otpctrl -w 0x5 0x8 0x0B0A0908
otpctrl -w 0x5 0xC 0x0F0E0D0C
otpctrl -w 0x6 0x0 0x13121110
otpctrl -w 0x6 0x4 0x17161514
otpctrl -w 0x6 0x8 0x1B1A1918
otpctrl -w 0x6 0xC 0x1F1E1D1C
The programming operation for 8 AES128 keys or 4 AES256 keys is similar.
2.1.5 AES Key Write Protection and Read Protection (OTP_AES128_KEY1~8_LOCK: 0xD,0xF,0x11,0x13,0x15,0x17,0x19,0x1B / OTP_AES128_KEY1~8_BLOCK: 0xE,0x10,0x12,0x14,0x16,0x18,0x1A,0x1C)¶
Optional operation, customers can use as needed.
Confirm LOCK and BLOCK of the first AES128 key (effective on next boot):
otpctrl -w 0xD 0x0 0xFFFFFFFF
otpctrl -w 0xE 0x0 0xFFFFFFFF
Check if LOCK and BLOCK of the first AES128 key are enabled:
otpctrl -r 0xD
otpctrl -r 0xE
Confirm LOCK and BLOCK of the first AES256 key (effective on next boot):
otpctrl -w 0xD 0x0 0xFFFFFFFF
otpctrl -w 0xF 0x0 0xFFFFFFFF
otpctrl -w 0xE 0x0 0xFFFFFFFF
otpctrl -w 0x10 0x0 0xFFFFFFFF
Check if LOCK and BLOCK of the first AES256 key are enabled:
otpctrl -r 0xD
otpctrl -r 0xF
otpctrl -r 0xE
otpctrl -r 0x10
The LOCK and BLOCK operations for 8 AES128 keys or 4 AES256 keys are similar.
2.1.6 Select IPL Decryption Key (OTP_ROM_SEL_AESKEY: 0x24)¶
If customers use the signature + encryption function of security boot, programming OTP_ROM_SEL_AESKEY to select which AES key in OTP to decrypt IPL is a necessary operation.
If customers only use security boot signature, do not program OTP_ROM_SEL_AESKEY.
Example:
-
Select AESKEY128_1
otpctrl -w 0x24 0x0 0xFF000000 -
Select AESKEY128_2
otpctrl -w 0x24 0x0 0xFF0000FF -
Select AESKEY128_3
otpctrl -w 0x24 0x0 0xFF00FF00 -
Select AESKEY128_4
otpctrl -w 0x24 0x0 0xFF00FFFF -
Select AESKEY128_5
otpctrl -w 0x24 0x0 0xFFFF0000 -
Select AESKEY128_6
otpctrl -w 0x24 0x0 0xFFFF00FF -
Select AESKEY128_7
otpctrl -w 0x24 0x0 0xFFFFFF00 -
Select AESKEY128_8
otpctrl -w 0x24 0x0 0xFFFFFFFF
Additionally, IPL can use AES256 decryption. AESKEY256 in OTP is actually composed of two AES128 keys in OTP. The composition and setting examples are as follows:
-
Select AESKEY256_1 (Composition mode: AES128key1 + AES128key2)
otpctrl -w 0x24 0x0 0x00FF0000 -
Select AESKEY256_2 (Composition mode: AES128key3 + AES128key4)
otpctrl -w 0x24 0x0 0x00FF00FF -
Select AESKEY256_3 (Composition mode: AES128key5 + AES128key6)
otpctrl -w 0x24 0x0 0x00FFFF00 -
Select AESKEY256_4 (Composition mode: AES128key7 + AES128key8)
otpctrl -w 0x24 0x0 0x00FFFFFF
2.1.7 IPL Decryption Key Selection Write Protection (OTP_ROM_SEL_AESKEY_LOCK: 0x25)¶
Optional operation, customers can use as needed.
Confirm LOCK the content in OTP_ROM_SEL_AESKEY (effective on next boot):
otpctrl -w 0x25 0x0 0xFFFFFFFF
Check if LOCK is enabled:
otpctrl -r 0x25
2.1.8 RSA Key Length Configuration (OTP_RSA_KEY_LEN: 0x2F)¶
If customers use rsa4096 for signing, this OTP field must be programmed. No need to pay attention if using rsa2048.
otpctrl -w 0x2F 0x0 0xFFFFFFFF
2.2 OTP Fields Related to Fault Injection and Signal Analysis Prevention¶
Usage Scenario: Enhance the system's hardware security protection capabilities to prevent obtaining sensitive information or damaging system functions through physical attack means (such as fault injection, side-channel attacks). Suitable for applications with extremely high security requirements.
For IFord system chips, if customers use fault injection and signal analysis prevention functions (Multiple Round, SCA, key2sha1), they need to pay attention to the following OTP contents:
| OTP | command ID | length(byte) | Permission | Description |
|---|---|---|---|---|
| OTP_PROTECT_ENABLE | 0x30 | 4 | Read/Write | Master switch for rsa2sha1, pwd2sha1 and aes2sha1 |
| OTP_RSA_KEY_N_CHK_ENABLE | 0x31 | 4 | Read/Write | Sub-switch to enable rsa2sha1, indicates to start RSA public key check function |
| OTP_PASSWORD_CHK_ENABLE | 0x32 | 4 | Read/Write | Sub-switch to enable pwd2sha1, indicates to start password check function |
| OTP_OTP_KEY_CHK_ENABLE | 0x33 | 4 | Read/Write | Sub-switch to enable aes2sha1, indicates to start AES key check function |
| OTP_AES_MULTIPLE_NUM | 0x34 | 8 | Read/Write | Switch to enable aes multiple num, indicates AES internal encryption/decryption needs to be done N(1~4) times, output only after N results are consistent |
| OTP_SCA_PROTECT_ENABLE | 0x35 | 4 | Read/Write | Switch to enable SCA PROTECT, indicates adding random number in HW aes encryption/decryption to disrupt AES timing, preventing signal analysis |
| OTP_PassWord_chk | 0x36 | 4 | Read/Write | Save SHA1&XOR calculation value of PASSWORD, used to verify OTP PASSWORD reliability during boot process |
| OTP_Key1_chk | 0x37 | 4 | Read/Write | Save SHA1&XOR calculation value of 1st AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_Key2_chk | 0x38 | 4 | Read/Write | Save SHA1&XOR calculation value of 2nd AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_Key3_chk | 0x39 | 4 | Read/Write | Save SHA1&XOR calculation value of 3rd AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_Key4_chk | 0x3A | 4 | Read/Write | Save SHA1&XOR calculation value of 4th AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_Key5_chk | 0x3B | 4 | Read/Write | Save SHA1&XOR calculation value of 5th AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_Key6_chk | 0x3C | 4 | Read/Write | Save SHA1&XOR calculation value of 6th AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_Key7_chk | 0x3D | 4 | Read/Write | Save SHA1&XOR calculation value of 7th AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_Key8_chk | 0x3E | 4 | Read/Write | Save SHA1&XOR calculation value of 8th AES128, used to verify OTP AESKEY reliability during boot process |
| OTP_RSA_KEY_N_CHK | 0x3F | 4 | Read/Write | Save SHA1&XOR calculation value of RSA public N key, used to verify OTP RSAKEY reliability during boot process |
The programming methods for each OTP field are illustrated as follows.
2.2.1 Enable Protection Function Master Switch (OTP_PROTECT_ENABLE: 0x30)¶
Enable the master switch for aes2sha1 pwd2sha1 rsa2sha1 check, effective on next boot after programming.
otpctrl -w 0x30 0x0 0xFFFFFFFF
Check if the master switch is enabled:
otpctrl -r 0x30
2.2.2 RSA Public Key Integrity Check (OTP_RSA_KEY_N_CHK_ENABLE: 0x31, OTP_RSA_KEY_N_CHK: 0x3F)¶
Optional operation, customers can use as needed. Note that enabling OTP_RSA_KEY_N_CHK_ENABLE requires programming OTP_RSA_KEY_N_CHK.
For existing rsa-public.pem files, the key-SHA1 production method is as follows:
./key_proc.py --key2sha1 -f rsa2048/public-otp.pem
------------------------------------------------------>public-otp.pem_sha1.txt
For example, the content of pem_sha1.txt converted from an existing PEM file is as follows:
otpctrl -w 0x3F 0x0 0xa44a2887
Then enable the rsa2sha1 sub-switch:
otpctrl -w 0x31 0x0 0xFFFFFFFF
2.2.3 Password Integrity Check (OTP_PASSWORD_CHK_ENABLE: 0x32, OTP_PassWord_chk: 0x36)¶
Optional operation, customers can use as needed. Note that enabling OTP_PASSWORD_CHK_ENABLE requires programming OTP_PassWord_chk.
For existing pwd.bin files, the key-SHA1 production method is as follows:
./key_proc.py --pwd2sha1 -f pwd.bin
------------------------------------------------------>pwd.bin_sha1.txt
For example, the content of bin_sha1.txt converted from an existing pwd.bin file is as follows:
otpctrl -w 0x36 0x0 0xa6a938d1
Then enable the pwd2sha1 sub-switch:
otpctrl -w 0x32 0x0 0xFFFFFFFF
2.2.4 AES Key Integrity Check (OTP_OTP_KEY_CHK_ENABLE: 0x33, OTP_Key1~8_chk: 0x37-0x3E)¶
Optional operation, customers can use as needed. Note that enabling OTP_OTP_KEY_CHK_ENABLE requires programming the OTP_Key_chk corresponding to the nth AES key specified by OTP_ROM_SELECT_AES_KEY.
For existing aesKey.bin files, the key-SHA1 production method is as follows:
./key_proc.py --key2sha1 -f aeskey/aesKey1.bin
------------------------------------------------------>aesKey1.bin_sha1.txt
For example, the content of bin_sha1.txt converted from an existing aesKey.bin file is as follows:
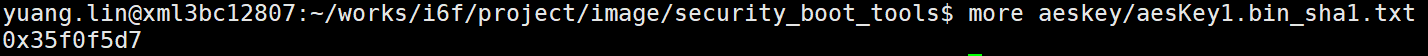
If the AESKey used by AESDMA specified by OTP_ROM_SELECT_AES_KEY is the 1st one, program the content of bin_sha1.txt to OTP_Key1_chk
otpctrl -w 0x37 0x0 0x35f0f5d7
If the AESKey used by AESDMA specified by OTP_ROM_SELECT_AES_KEY is the 2nd one, program the content of bin_sha1.txt to OTP_Key2_chk
otpctrl -w 0x38 0x0 0x35f0f5d7
If the AESKey used by AESDMA specified by OTP_ROM_SELECT_AES_KEY is the 3rd one, program the content of bin_sha1.txt to OTP_Key3_chk
otpctrl -w 0x39 0x0 0x35f0f5d7
And so on.
Then enable the aes2sha1 sub-switch:
otpctrl -w 0x33 0x0 0xFFFFFFFF
2.2.5 AES Multiple Encryption Configuration (OTP_AES_MULTIPLE_NUM: 0x34)¶
Optional operation, customers can use as needed. Indicates that AES internal encryption/decryption needs to be done N(1~4) times, output only after N results are consistent. After setting this Command, it will be effective on next boot.
Example:
MULTIPLE_NUM=1:
otpctrl -w 0x34 0x0 0x00000000
otpctrl -w 0x34 0x4 0x00000000
MULTIPLE_NUM=2:
otpctrl -w 0x34 0x0 0xFFFFFFFF
otpctrl -w 0x34 0x4 0x00000000
MULTIPLE_NUM=3:
otpctrl -w 0x34 0x0 0x00000000
otpctrl -w 0x34 0x4 0xFFFFFFFF
MULTIPLE_NUM=4:
otpctrl -w 0x34 0x0 0xFFFFFFFF
otpctrl -w 0x34 0x4 0xFFFFFFFF
2.2.6 Side Channel Attack Protection (OTP_SCA_PROTECT_ENABLE: 0x35)¶
Optional operation, customers can use as needed. Indicates to enable SCA PROTECT. SCA adds random numbers in AES encryption/decryption to disrupt AES timing, preventing signal analysis. After setting this Command, it will be effective on next boot.
Example:
WRITE COMMAND: otpctrl -w 0x35 0x0 0xFFFFFFFF
2.3 OTP Fields Related to User Custom Data¶
Usage Scenario: Store product-specific configuration information, serial numbers, calibration parameters, license information and other user-defined data. Provides 1KB of storage space with support for regional write protection.
For IFord system chips, OTP area has 8K bits open for customers to use to save custom data.
| OTP | command ID | length(byte) | Permission | Description |
|---|---|---|---|---|
| OTP_CUSTOMER_AREA | 0XA0 | 1024 | Read/Write | Available for users to freely program custom data |
| OTP_CUSTOMER_AREA_LOCK0 | 0XA1 | 4 | Read/Write | After LOCK, 0-127Bytes custom data cannot be modified |
| OTP_CUSTOMER_AREA_LOCK1 | 0XA2 | 4 | Read/Write | After LOCK, 128-255Bytes custom data cannot be modified |
| OTP_CUSTOMER_AREA_LOCK2 | 0XA3 | 4 | Read/Write | After LOCK, 256-383Bytes custom data cannot be modified |
| OTP_CUSTOMER_AREA_LOCK3 | 0XA4 | 4 | Read/Write | After LOCK, 384-511Bytes custom data cannot be modified |
| OTP_CUSTOMER_AREA_LOCK4 | 0XA5 | 4 | Read/Write | After LOCK, 512-639Bytes custom data cannot be modified |
| OTP_CUSTOMER_AREA_LOCK5 | 0XA6 | 4 | Read/Write | After LOCK, 640-767Bytes custom data cannot be modified |
| OTP_CUSTOMER_AREA_LOCK6 | 0XA7 | 4 | Read/Write | After LOCK, 768-895Bytes custom data cannot be modified |
| OTP_CUSTOMER_AREA_LOCK7 | 0XA8 | 4 | Read/Write | After LOCK, 896-1023Bytes custom data cannot be modified |
The programming methods for each OTP field are illustrated as follows.
2.3.1 User Custom Data Storage (OTP_CUSTOMER_AREA: 0xA0)¶
Only 4 bytes can be written at a time. Offset ranges from 0x0 - 0x3FF.
Example:
otpctrl -w 0xA0 0x0 0x12345678
otpctrl -w 0xA0 0x4 0x09ABCDEF
otpctrl -w 0xA0 0x8 0x33445566
And so on.
Last 4 bytes WRITE COMMAND:
otpctrl -w 0xA0 0x3fC 0xAA778899
CUSTOMER_AREA read:
otpctrl -r 0xA0
2.3.2 User Data Area Write Protection (OTP_CUSTOMER_AREA_LOCK: 0xA1~0xA8)¶
LOCK 0k~1K bits data (effective on next boot):
otpctrl -w 0xA1 0x0 0xFFFFFFFF
LOCK 1k~2K bits data (effective on next boot):
otpctrl -w 0xA2 0x0 0xFFFFFFFF
LOCK 2k~3K bits data (effective on next boot):
otpctrl -w 0xA3 0x0 0xFFFFFFFF
LOCK 3k~4K bits data (effective on next boot):
otpctrl -w 0xA4 0x0 0xFFFFFFFF
LOCK 4k~5K bits data (effective on next boot):
otpctrl -w 0xA5 0x0 0xFFFFFFFF
LOCK 5k~6K bits data (effective on next boot):
otpctrl -w 0xA6 0x0 0xFFFFFFFF
LOCK 6k~7K bits data (effective on next boot):
otpctrl -w 0xA7 0x0 0xFFFFFFFF
LOCK 7k~8K bits data (effective on next boot):
otpctrl -w 0xA8 0x0 0xFFFFFFFF
2.4 Password Mode Related Fields¶
Usage Scenario: Control access permissions for debug interfaces (JTAG, I2C), prevent unauthorized debug access through password protection mechanism, protect product intellectual property and sensitive information.
| OTP | command ID | length(byte) | Permission | Description |
|---|---|---|---|---|
| OTP_DISABLE_JTAG_MODE | 0X1F | 4 | Read/Write | Used to permanently disable JTAG mode |
| OTP_PASSWORD_JTAG_MODE | 0X20 | 4 | Read/Write | Set protection mode, requires correct password to open JTAG mode |
| OTP_PASSWORD | 0x21 | 8 | Read/Write | Debugging Ports(I2C/eJTAG) password |
| OTP_PASSWORD_LOCK | 0x22 | 4 | Read/Write | LOCK action for PASSWORD field in OTP, cannot be modified after LOCK, customers can use as needed |
| OTP_PASSWORD_BLOCK | 0x23 | 4 | Read/Write | BLOCK action for PASSWORD field in OTP, CPU cannot read PASSWORD from OTP after BLOCK, customers can use as needed |
| OTP_DISABLE_IIC_MODE | 0X50 | 4 | Read/Write | Used to permanently disable IIC mode |
| OTP_PASSWORD_IIC_MODE | 0X51 | 4 | Read/Write | Set protection mode, requires correct password to open IIC mode |
2.4.1 Permanently Disable JTAG Debug Interface (OTP_DISABLE_JTAG_MODE: 0x1F)¶
Permanently disable JTAG debug port (effective on next boot):
otpctrl -w 0x1F 0x0 0xFFFFFFFF
2.4.2 Set JTAG Password Protection Mode (OTP_PASSWORD_JTAG_MODE: 0x20)¶
Set protection mode, requires correct password to open JTAG debug port (effective on next boot):
otpctrl -w 0x20 0x0 0xFFFFFFFF
2.4.3 Configure Debug Password (OTP_PASSWORD: 0x21)¶
Set by user, this field is used to set the password for protection mode (effective on next boot):
otpctrl -w 0x21 0x0 0xXXXXXXXX
otpctrl -w 0x21 0x4 0xXXXXXXXX
2.4.4 Debug Password Write Protection (OTP_PASSWORD_LOCK: 0x22)¶
LOCK the PASSWORD field of OTP (effective on next boot):
otpctrl -w 0x22 0x0 0xFFFFFFFF
2.4.5 Block Debug Password Access (OTP_PASSWORD_BLOCK: 0x23)¶
BLOCK the PASSWORD field of OTP (effective on next boot):
otpctrl -w 0x23 0x0 0xFFFFFFFF
2.4.6 Permanently Disable IIC Debug Interface (OTP_DISABLE_IIC_MODE: 0x50)¶
Permanently disable IIC debug port (effective on next boot):
otpctrl -w 0x50 0x0 0xFFFFFFFF
2.4.7 Set IIC Password Protection Mode (OTP_PASSWORD_IIC_MODE: 0x51)¶
Set protection mode, requires correct password to open IIC debug port (effective on next boot):
otpctrl -w 0x51 0x0 0xFFFFFFFF
2.5 ID Related OTP Fields¶
Usage Scenario: Read device unique identifiers and identity information for device identity authentication, serial number management, anti-counterfeiting identification and other applications. These identifiers are solidified during production and can only be read, not modified.
| OTP | command ID | length(byte) | Permission |
|---|---|---|---|
| OTP_UUID2 | 0X26 | 8 | Read-Only |
| OTP_DID1 | 0X27 | 8 | Read-Only |
| OTP_DID2 | 0X29 | 8 | Read-Only |
| OTP_UUID | 0X2E | 8 | Read-Only |
2.5.1 Read Device Unique Identifier 2 (OTP_UUID2: 0x26)¶
otpctrl -r 0x26
2.5.2 Read Device Identifier 1 (OTP_DID1: 0x27)¶
otpctrl -r 0x27
2.5.3 Read Device Identifier 2 (OTP_DID2: 0x29)¶
otpctrl -r 0x29
2.5.4 Read Device Unique Identifier 1 (OTP_UUID1: 0x2E)¶
otpctrl -r 0x2E
2.6 Other OTP Fields¶
Usage Scenario: System-level configuration options, including boot mode selection, secure area configuration, force boot mode, etc. These configurations affect the system's boot behavior and runtime environment.
| OTP | command ID | length(byte) | Permission | Description |
|---|---|---|---|---|
| OTP_FORCE_UARTBOOT | 0X2D | 8 | Read/Write | Force ROM to use UART boot mode |
| OTP_TZ | 0X40 | 4 | Read/Write | Default is 0, set to 1 to enable TZ |
| OTP_BOOT_SOURCE | 0XA9 | 4 | Read/Write | After OTP_BOOT_SOURCE_ENABLE is set to 1, determine the specific boot mode through this field |
| OTP_BOOT_SOURCE_ENABLE | 0XAA | 4 | Read/Write | 0 corresponds to hardware boot, 1 corresponds to determining boot mode through OTP_BOOT_SOURCE field |
| OTP_BOOT_SOURCE_LOCK | 0XAB | 4 | Read/Write | LOCK action for OTP_BOOT_SOURCE field in OTP, cannot be modified after LOCK, customers can use as needed |
2.6.1 Force UART Boot Mode (OTP_FORCE_UARTBOOT: 0x2D)¶
Default is not to force ROM to use UARTBOOT mode. If you need to force UARTBOOT mode, use the following command (effective on next boot):
otpctrl -w 0x2D 0x0 0x00000000
otpctrl -w 0x2D 0x4 0xFFFFFFFF
otpctrl -w 0x2D 0x0 0xFFFFFFFF
otpctrl -w 0x2D 0x4 0x00000000
If you need to restore to default state, use the following command (effective on next boot):
otpctrl -w 0x2D 0x0 0xFFFFFFFF
otpctrl -w 0x2D 0x4 0xFFFFFFFF
View current FORCE UARTBOOT status:
otpctrl -r 0x2D
2.6.2 TrustZone Security Area Configuration (OTP_TZ: 0x40)¶
Set Trust Zone switch, usually set in product phase (effective on next boot):
otpctrl -w 0x40 0x0 0xFFFFFFFF
Check current TZ status:
otpctrl -r 0x40
2.6.3 Boot Source Selection Configuration (OTP_BOOT_SOURCE: 0xA9)¶
After OTP_BOOT_SOURCE_ENABLE is set to 1, determine the boot mode through this field:
SPI NAND:
otpctrl -w 0xA9 0x0 0x00000f00
SPI NAND (skip SD):
otpctrl -w 0xA9 0x0 0x00000f0f
SPI NOR:
otpctrl -w 0xA9 0x0 0x00000ff0
SPI NOR (skip SD):
otpctrl -w 0xA9 0x0 0x00000fff
USB2.0:
otpctrl -w 0xA9 0x0 0x00000000
UART:
otpctrl -w 0xA9 0x0 0x0000000f
eMMC 4-bit:
otpctrl -w 0xA9 0x0 0x000000ff
2.6.4 Enable OTP Boot Source Selection (OTP_BOOT_SOURCE_ENABLE: 0xAA)¶
Determine boot mode through OTP_BOOT_SOURCE field:
otpctrl -w 0xAA 0x0 0xFFFFFFFF
2.6.5 Boot Source Configuration Write Protection (OTP_BOOT_SOURCE_LOCK: 0xAB)¶
LOCK the BOOT_SOURCE field of OTP (effective on next boot):
otpctrl -w 0xAB 0x0 0xFFFFFFFF